Digital Signage Company
Take your business to the next level with MetroClick’s digital signage solutions. Our touch screen kiosks are designed with the latest technology to provide your customers with an interactive and engaging experience.

Trusted by industry leaders to power better customer experiences

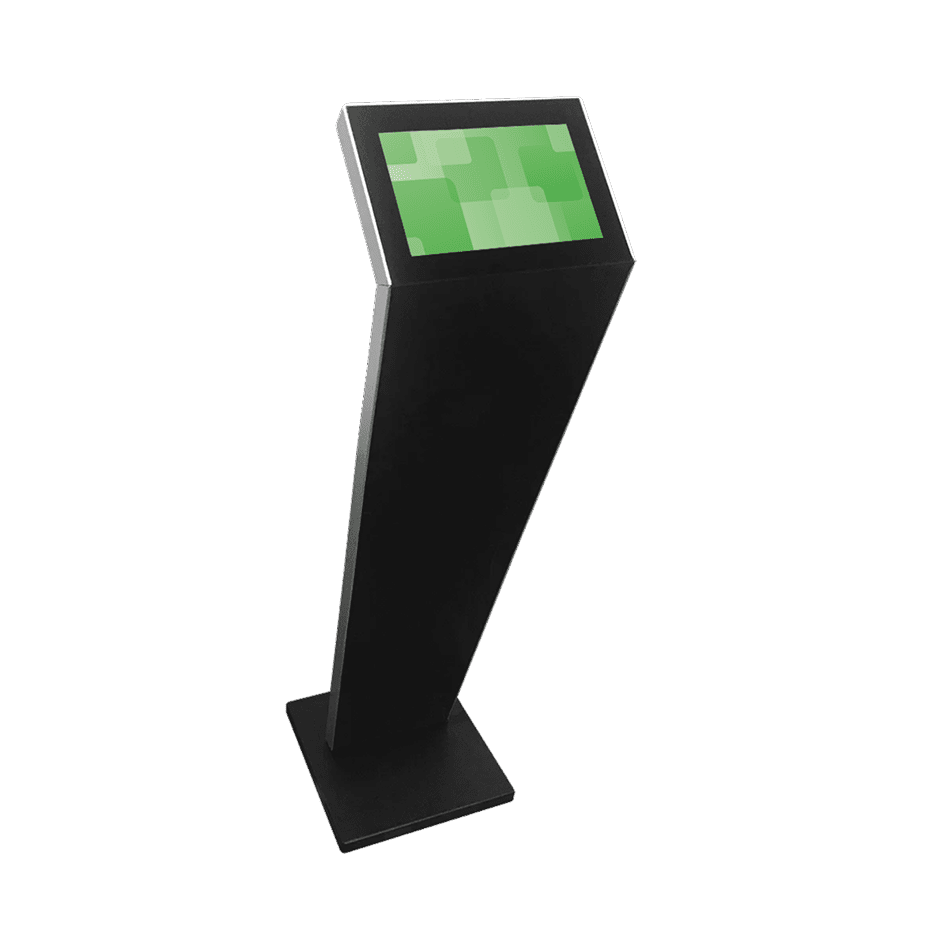
Strip-Type Displays

Digital Signage A-Frame
Large Touch Screens
Discover the versatility built into our digital signage products
Built for Every Environment
Trust in ruggedized, rated, reliable and robust devices of all shapes and sizes that perform flawlessly indoors or out.
Engage and Inform
Guide users through effortless, self-driven, interactive experiences or stream advertisements and promotions 24/7 on optically bonded, enhanced viewing touch screens.
Modular in Design
Easily configure, connect and scale devices to suit different locations, functions and use cases, while streamlining maintenance, serviceability and operational expenses.
Unapologetically Authentic
Fit any space with aesthetics and branding that drives emotional resonance and authentic connections to your true brand.
Industry applications for Digital Signage
Sports Arenas
Guide fans from parking to seats
Interactive paths that simplify navigation and amplify sponsor engagement
Healthcare Facilities
Simplify complex patient journeys
Real-time wayfinding that adapts to emergencies and staffing changes
Retail Spaces
Convert browsers to buyers
Shelf-edge experiences that bridge digital browsing and physical products
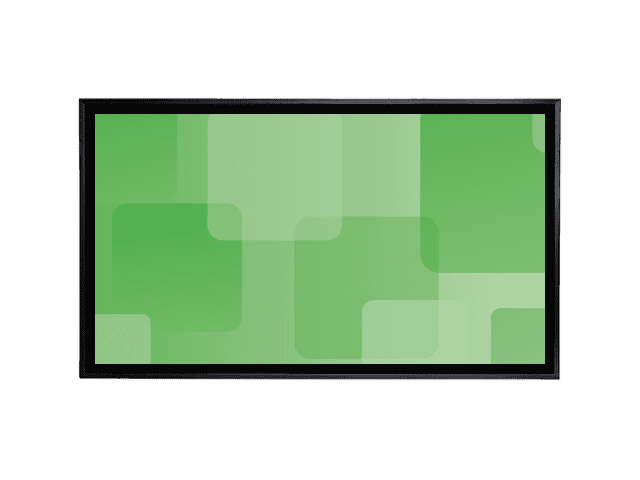
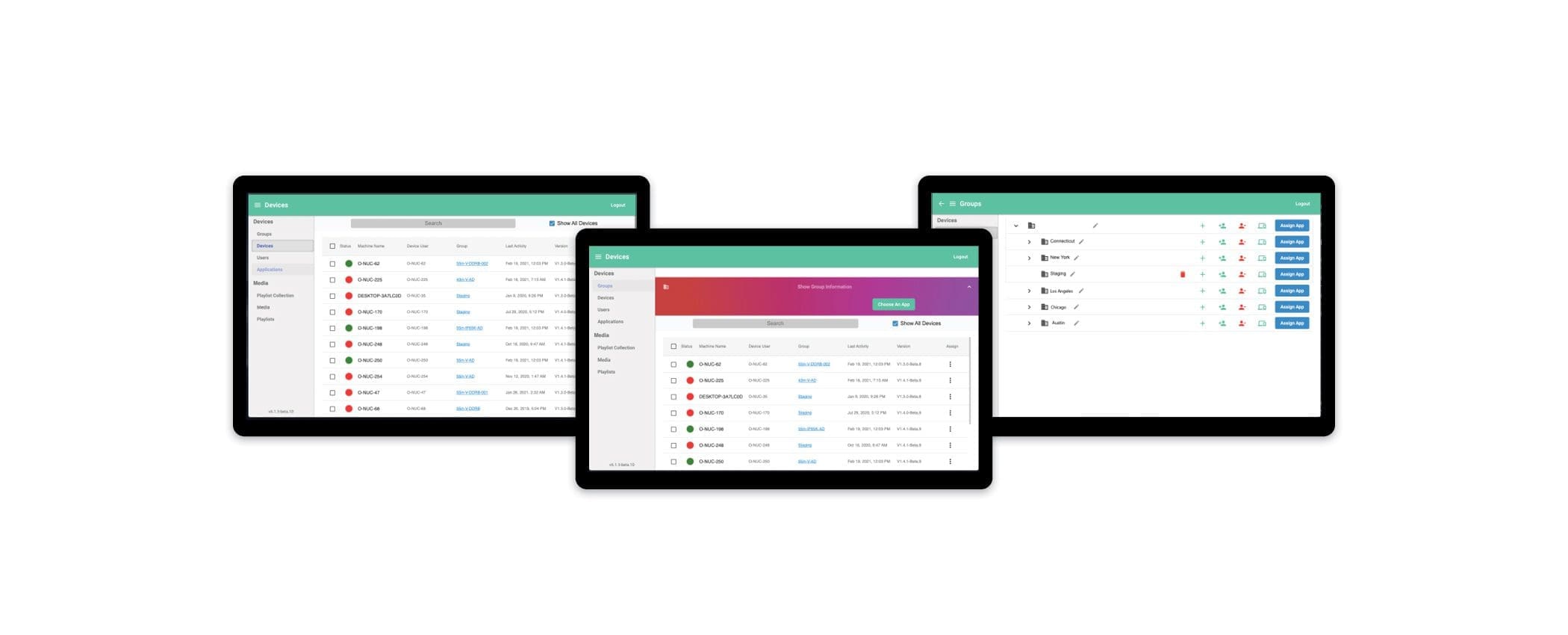
MetroClick Manager
Sync every screen, everywhere
Our hybrid CMS and DXP platform that seamlessly connects your digital experiences. Easily deliver omnichannel content using intuitive editing tools and templates to craft engaging customer interactions.
Other hardware options
Small Format Kiosks

Transactional Kiosks
Immersive Kiosks
More Information
Why Businesses Choose MetroClick for Digital Signage
Most digital signage companies sell you software and tell you to figure out the hardware yourself. MetroClick is different — we design, manufacture, and install complete digital signage solutions from our facility in New York City. One vendor for the screens, the digital signage software, the hardware, and the on-site installation. When something needs attention, you call one number — not three.
Since 2012, MetroClick has deployed digital signage across 180+ countries for brands in retail, hospitality, healthcare, corporate, entertainment, and restaurants. Every screen ships pre-configured with your content, your branding, and your CMS — plug it in and it’s live.
Digital Signage Products: Screens, Video Walls, and More
MetroClick manufactures commercial-grade digital signage screens and displays built for 24/7 operation — not consumer TVs repurposed for business use. Our screens feature antimicrobial coatings, high-resolution panels, and integrated media players designed to run for years without failure.
Screen Sizes and Form Factors
- Countertop displays (7″ – 15″) — Point-of-sale screens, checkout prompts, tabletop menus, and customer feedback tools
- Wall-mounted screens (22″ – 55″) — Lobby directories, menu boards, promotional displays, and wayfinding signage for offices, restaurants, and retail spaces
- Floor-standing kiosks (32″ – 65″) — Self-service check-in, information kiosks, interactive product catalogs, and touchscreen kiosks
- Large-format displays (65″ – 98″) — Conference rooms, trade show booths, storefront windows, and high-impact promotional walls. Available in LED and OLED signage panels for ultra-thin profiles and stunning contrast. LG digital signage OLED displays and more available in select configurations
- Video walls — Multi-screen video wall arrays with ultra-narrow bezels for lobbies, command centers, and event venues. Video wall configurations from 2×2 to custom sizes, powered by commercial video wall processors. Video wall content managed through the same CMS as all your other screens
- Outdoor digital signage — Weatherproof, high-brightness screens rated for direct sunlight, rain, and temperature extremes. IP65-rated enclosures with automatic brightness control
- Digital mirrors — Interactive mirror displays for retail fitting rooms, hospitality, and experiential marketing
- Digital sandwich boards — Portable sidewalk-facing signage for restaurants, retail, and events
Display Technology Options
MetroClick offers multiple display panel technologies to match your business goals, environment, and budget:
- LED signage — High brightness, energy-efficient, ideal for outdoor signage and large-format displays where visibility is critical
- OLED signage — Ultra-thin panels with perfect blacks and wide viewing angles for premium retail and hospitality spaces. LG digital signage OLED panels available in select configurations
- LCD commercial displays — Cost-effective, reliable, available in every size from 7″ to 98″ with 4K resolution options
- Interactive touch overlays — Capacitive and infrared touch technology layered onto any display for user experience-focused applications like wayfinding, product browsing, and self-service
Hardware Features and Peripherals
Every MetroClick screen can be configured with optional peripherals and connectivity features for interactive and transactional use cases:
- Touch technology — Capacitive or infrared overlays supporting multi-touch gestures and control
- Payment processing — Integrated EMV chip readers, NFC/contactless tap-to-pay, and mobile wallet support for payment kiosks
- Cameras and sensors — Built-in cameras for video conferencing, audience analytics, and QR code scanning
- RFID and NFC readers — Employee badge scanning, loyalty card reading, and asset tracking
- Printers — Receipt, badge, and ticket printers for self-service items and check-in apps
- Connectivity — Wi-Fi, Ethernet, Bluetooth, and optional cellular for outdoor and remote locations. All players connect to your CMS via web browser-based dashboard. Compatible with most TV screens and commercial displays
- Media player — Integrated Android, Windows, or Linux media player with SoC (system-on-chip) options. Supports all major operating systems and file formats for video, images, and playback of playlists
- Audio — Integrated speakers for video playback, alerts, and accessibility
Need a fully custom kiosk configuration? MetroClick builds to spec — tell us what tools and features you need and we’ll design the box. Our content management software powers everything from a single TV in your lobby to a video wall spanning an entire storefront.
Digital Signage Software and CMS
Every MetroClick screen ships with cloud-based digital signage software that gives you full control over content across all your screens and locations. The content management system (CMS) includes:
- Drag-and-drop content editor — Build layouts with video, images, text, social media feeds, YouTube, Instagram, weather widgets, and more. No design skills required
- Playlist scheduling — Create playlists of content and schedule playback by time of day, day of week, or specific dates. Automate menu boards, promotions, and announcements
- Multi-screen management — Control one screen or thousands from a single dashboard. Group screens by location, department, or campaign for easy setup and updates
- Remote monitoring — Track screen status, connectivity, and content playback from anywhere via web browser. Get alerts when a device goes offline
- User roles and permissions — Grant access by role so marketing teams, store managers, and IT admins each see the features and screens relevant to them
- Analytics and reporting — Measure content play counts, audience attention, and engagement to drive data-backed decisions
- App integrations — Connect to Google, social media, RSS feeds, calendars, and enterprise apps to display live data automatically
How Digital Signage Installation Works
MetroClick handles the entire process so your team can focus on business goals instead of coordinating vendors:
- Consultation and design — Tell us about your spaces, your goals, and your budget. We recommend screen sizes, mounting options, and software features for your use case. For multi-location rollouts, we conduct site surveys to ensure consistent installation
- Manufacturing and configuration — We build your screens, pre-load the digital signage software, configure your branding and initial content, and test everything before shipping
- Nationwide installation — Our team handles mounting, cabling, network connection, and final testing on-site. We service all 50 states and international locations
- Ongoing management and support — After setup, manage all your screens from the cloud CMS. MetroClick provides ongoing support, warranty service, and hardware replacement
Industries Using Digital Signage
MetroClick provides digital signage solutions tailored to the needs of each industry:
- Retail — In-store promotions, interactive product catalogs, self-checkout screens, and digital advertising displays for shoppers
- Restaurants and bars — Digital menu boards, self-service ordering kiosks, and promotional TV screens
- Hospitality — Hotel lobby directories, concierge kiosks, conference room signage, and guest check-in
- Healthcare — Patient check-in kiosks, wayfinding screens, waiting room displays, and safety announcements
- Corporate — Meeting room displays, lobby visitor management, employee announcements, and campus directories
- Entertainment — Venue wayfinding, interactive exhibits, event schedules, and immersive experiences
- Industrial — Factory floor dashboards, safety alerts, and production metrics for employees
- Real estate — Property listing displays, interactive floor plans, and building directories
- Travel and transportation — Airport wayfinding, transit schedule boards, and advertising screens
- Sports venues — Scoreboard integration, fan engagement, and concession menus
Digital Signage vs Traditional Printed Signs
Still evaluating the choice between digital and traditional printed signage? Here’s how they compare:
| Feature | Traditional Printed Signs | Digital Signage Displays |
|---|---|---|
| Content updates | Print and ship new materials (days/weeks) | Update remotely in seconds from any device |
| Ongoing cost | Reprinting for every change | Software subscription + power |
| Content types | Static images and text only | Video, animation, live data, apps, social media, playlists |
| Scheduling | Manual swap by staff | Automated scheduling and playlists via CMS |
| Analytics | None | Play counts, attention tracking, reviews of performance |
| Multi-location control | Ship materials to each place individually | Push content to all screens from one account |
| Sustainability | Paper waste with every update | Zero waste — all changes are digital |
| Interactivity | Passive viewing only | Touch, gesture, mobile, QR codes, payments — full user experience |
Digital signage typically pays for itself within 6-12 months through reduced printing costs, faster content updates, and measurable increases in sales and customer action.
Digital Signage Rental for Events
Not ready to buy? MetroClick offers digital signage rentals for trade shows, conferences, product launches, pop-up retail, and temporary installations. Rental packages include the screens, media players, content setup, delivery, and on-site technical support. Rent for a day, a week, or a season.
Get Started with MetroClick Digital Signage
Whether you need one screen for your lobby or a network across hundreds of locations, MetroClick designs, manufactures, and installs digital signage solutions that work from day one. Tell us about your business goals and we’ll recommend the right screens, digital signage software, and setup for your budget. Learn more about our digital signage software, browse our hardware catalog, or explore indoor and outdoor digital signage options.